The integration of the Internet into our daily lives has made accessing of data an effortless activity, in turn making our lives undeniably easier. However, sharing our data publicly or privately has its risks and consequences, especially when data is misused. You’ll never really know where your data might end up. This is where data privacy and cybersecurity come in.
With the theme “Supercharge Your Data Privacy and Cyber Security Program”, Data Privacy Asia Manila brought a great lineup of speakers from around the globe. This year’s conference focused on practical advice and implementation guides to help improve data privacy and cybersecurity programs.
5 Important Things I Learned During the DPA Manila 2018 Conference
5. Cybersecurity is important.
Data privacy and cyber-security should always be given great importance. Control over data has now become the next cold war. Pierre Noel, Chief Security and Privacy Officer (CSPO) and former GRAB advisor, states that cyber security is often overlooked by companies because of the cost associated with them, but this should not be the case because the cost of a lack in security could end up being more expensive.
Rebecca Herold of SIMBUS adds that “businesses and organizations that make privacy a goal will build emotional connections to their brand”. Making privacy a priority in businesses can equate to good customer trust. The loss of trust can result to less clients and low profit.
4. Personal data should be kept private.
Herold also discusses that privacy rules often develop when a problem arises with the breach and misuse of personal data. Herold defines personal data as “a partial representation of an actual human being.”
Increasing privacy of personal data literally increases the physical safety of an individual. A situational example of this is the data breach this year in Aultman Hospital in Ohio, USA which could have potentially stopped critical services, especially for patients on life support.
3. There is a difference between consent and notice.
Notice and consent are two entirely different things. Notice is something you give out publicly while consent is given personally. Consent should be asked from the clients if the company were to take data that is outside the scope of the terms and conditions of the contract. Notices are to be given out when there are changes, major or minor, in a contract.
2. Two-Factor Authentication should be implemented.
TFA is an extra layer of security that not only requires a username or password, but also a confirmation of information unique to a user. An example of TFA is receiving confirmation through email, receiving a token pass sent to your mobile number, or inputting information that only you would now.
A live poll was created through the conference’s mobile app to survey the percentage of companies who use TFA in their systems. It turned out that only a few local companies were using TFA. This all the more proves the current situation of the country’s cybersecurity and data privacy state.
1. Look into incident response techniques.
Paul Jackson, Managing Director and Asia-Pacific Leader for Kroll’s Cyber Risk Practice, talks about how Incident Response (IR) is all about learning lessons. Preserving as much evidence as you can after a cyber attack is crucial. “Criminals are smart,” says Jackson as they will take all of the opportunities they can get to erase their tracks.
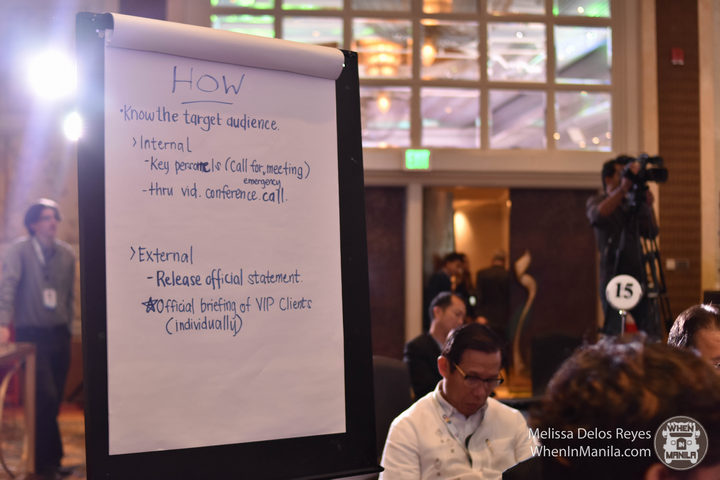
Jackson also discusses the importance of conducting tabletop exercises within the company, how it is better to make mistakes during exercises than in real life. A tabletop exercise is a meeting to discuss a simulated emergency situation like a cyber attack on the company’s system.
Roeland van Zeijst, a Global Cyber Security Strategist shares 5 strategies for data breach preparedness that companies can use:
- Be prepared – preparing a response during an attack is important to mitigate the impact of the cyber attack to the company.
- Check your defenses – running continuous tests on security helps in narrowing down the possible attacks the company might suffer.
- Let the white hats play (just a little bit) – white hats are the “good” hackers who find gaps in your system and informs the company about it. Though they do have good intentions, it’s best not to rely on them too much in finding faults in your system.
- Band together – good coordination within the teams in an organization is vital if cyber attacks should happen
- Customize – customize your plan to the company’s needs.
Even though the conference was geared towards the professional industry, I consider it a great privilege to have been able to attend and participate in this year’s Data Privacy Asia Manila conference. The valuable knowledge and techniques that I learned during the conference will not be put to waste for when I join the professional industry.
To learn more about the summit, visit www.ccap.ph and www.dataprivacyasia.com